[INDEX] What is the Single Digital Gateway (SDG) How the European Single Digital Gateway works Who the Single Digital Gateway is for Benefits of the Single Digital Gateway for citizens, businesses, and public administrations The role of the Single Digital Gateway in the European Union’s digital strategy Challenges and issues in implementing the Single Digital […]
Keycloak version 26.6: new features and improvements
[INDEX] Release 26.6 di Keycloak: novità e aggiornamenti JWT Authorization Grant Federated Client Authentication Keycloak 26.6 Orchestration and Workflows Zero-downtime patch releases Yookey: the IAM solution based on Keycloak Keycloak 26.6 release: new features and updates Keycloak has released new version 26.6 of its open-source platform dedicated to authentication and authorization management.This update introduces several […]
Identity Governance vs IAM: differences and how they integrate in IT security
[INDEX] What is Identity Governance (IGA)? What is Identity Management (IAM) and what it is used for How Access Governance works? Difference between Identity Governance and Identity Management Identity Governance and Identity Management: two complementary systems Yookey, the Identity & Access Management software What is Identity Governance (IGA) Identity Governance and Administration (IGA) is a […]
Data Security in Public Administration: the Key Role of IAM Systems
[INDEX] Authentication tools in Public Administration: MFA and SPID Real-Time Access Control: full audit and traceability IAM and Regulatory Compliance: GDPR, AgID and Public Data Security From Reactive Management to Proactive Security in Public Administrations Yookey: IAM Security for Municipalities, Public Structures and PA Institutions Authentication tools in Public Administration: MFA and SPID In Public […]
IAM and Security Incident Management
[INDEX] The role of IAM Systems in Incident Management Why IAM is a key element in cybersecurity incident IAM process in cybersecurity incident Tools and technologies for cybersecurity incidents in IAM Yookey: IAM’s response to Security challenges The role of IAM Systems in Incident Management Within incident management, IAM applies identity and access management processes […]
Privileged Access Management (PAM) and IAM: Security and Access Control
[INDEX] What is PAM (Privileged Access Management) and How It works Difference between IAM and PAM: A direct comparison When to use IAM and when to use PAM Integration between IAM and PAM: A Zero Trust approach PAM and IAM as compliance tools Yookey IAM Platform What is PAM (Privileged Access Management) and How It […]
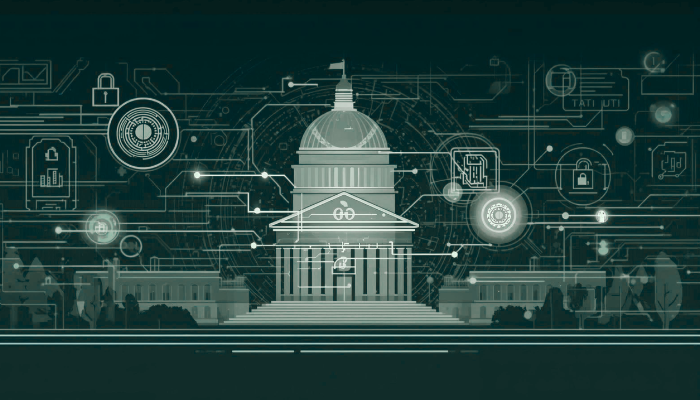
Attribute-Based Access Control (ABAC) and Role-Based Access Control (RBAC) compared
[INDEX] Permission Management: How ABAC and RBAC work Fundamental differences between ABAC and RBAC Policy Maintenance: ABAC Flexibility vs RBAC Stability Access Control Model Scalability: technical comparison between ABAC and RBAC Secure Access Management with Yookey Permission Management: How ABAC and RBAC work Attribute-Based Access Control (ABAC) ABAC uses an authorization model that takes into […]
IT Wallet and SPID: updates on digital identity
What is the IT Wallet and what is it for? How does the IT Wallet work and what can you do with the new digital wallet? Difference between SPID and IT Wallet: what changes for digital identity Difference between EUDI Wallet and IT Wallet Yookey IAM: simple integration of SPID and CIE What is the […]
SPID and CIE: differences and integration with Keycloak
INDEX SPID and CIE compared: how Digital Identities work SPID and CIE Security Levels Enabling SPID and CIE authentication through Keycloak May 2026 Update: SPID as the Authentication Standard for Digital Work Yookey ID: SPID and CIE Gateway SPID and CIE compared: how Digital Identities work Both SPID (Public Digital Identity System) and CIE (Electronic […]
Role-Based Access Control (RBAC): What is it, benefits and best practices
[INDEX] What is Role-Based Access Control (RBAC)? What are the benefits of implementing RBAC? What does the principle of least privilege mean in RBAC? Access Control with Yookey What is Role-Based Access Control (RBAC)? Role-Based Access Control (RBAC) constitutes a well-established access management model, which assigns authorizations not to individual users, but to the roles […]