IAM and Security Incident Management

The role of IAM Systems in Incident Management
Within incident management, IAM applies identity and access management processes to effectively support cybersecurity incident response activities.
When a security incident occurs, IAM systems focus on managing and securing compromised digital identities. Their role is critical in limiting the impact of the event and preventing further consequences or escalation of the breach.
This approach is structured to leverage IAM capabilities for rapid and effective intervention in response to signs of compromise, such as unusual behavior or unauthorized access, mitigating risk through immediate control of user credentials, privileges and permissions.
Why IAM is a key element in cybersecurity incident
An IAM system plays a strategic role in managing security incidents by providing full visibility and control over access. It enables precise monitoring of who accesses which resources, ensuring traceability and accountability.
In the event of an attack, it allows for rapid intervention by revoking or limiting compromised access, reducing the risk of lateral movement by attackers within the infrastructure.
The centralization of digital identities offers an additional advantage: it facilitates the quick detection of anomalies and breaches, while also supporting regulatory compliance requirements, such as those outlined in the NIS2 Directive and GDPR, through auditing, tracking, and forensic analysis capabilities.
Ready-Made Templates
Are you looking for an IAM system?Visit Yookey’s website to discover the available solutions.
IAM process in cybersecurity incident
When a compromised account is detected, an IAM-based response follows four key phases aimed at containing risk and restoring security.
- Isolation and Containment: The priority is to immediately limit the impact of the incident. This involves disabling the suspicious account, revoking active sessions, and blocking access from unrecognized IP addresses or devices, preventing further unauthorized use.
- Analysis and Identification: A thorough examination of access logs and recorded activity is conducted to reconstruct the attack’s dynamics — for example, phishing attempts — and to identify any lateral movement within the infrastructure.
- Recovery and Mitigation: Once the cause is understood, measures are taken to restore secure conditions: resetting credentials, reviewing assigned privileges to remove excessive permissions, and enabling multi-factor authentication (MFA) to strengthen account protection.
- Monitoring and Prevention: Finally, preventive measures are implemented to reduce the risk of recurrence. These include activating automatic alerts for suspicious behavior, updating security policies, and training users on common threat vectors.
Tools and technologies for cybersecurity incidents in IAM
An effective strategy relies on an integrated set of technologies capable of preventing, detecting and containing threats in a timely manner.
Among the most relevant preventive measures are Multi-Factor Authentication (MFA) and Single Sign-On (SSO), tools that significantly reduce the attack surface associated with password-only access, strengthening access control.
At the orchestration and response level, IAM integrates with monitoring and automation platforms such as:
- SIEM systems, which enable advanced collection and correlation of security logs;
- SOAR solutions, which allow corrective actions to be automated, such as the immediate blocking of a compromised account.
Finally, Identity Governance and Administration (IGA) platforms complete the technological ecosystem, supporting periodic access reviews and the timely revocation of obsolete or excessive privileges, thereby reducing the risk associated with unnecessary authorizations.
Yookey: IAM’s response to Security challenges
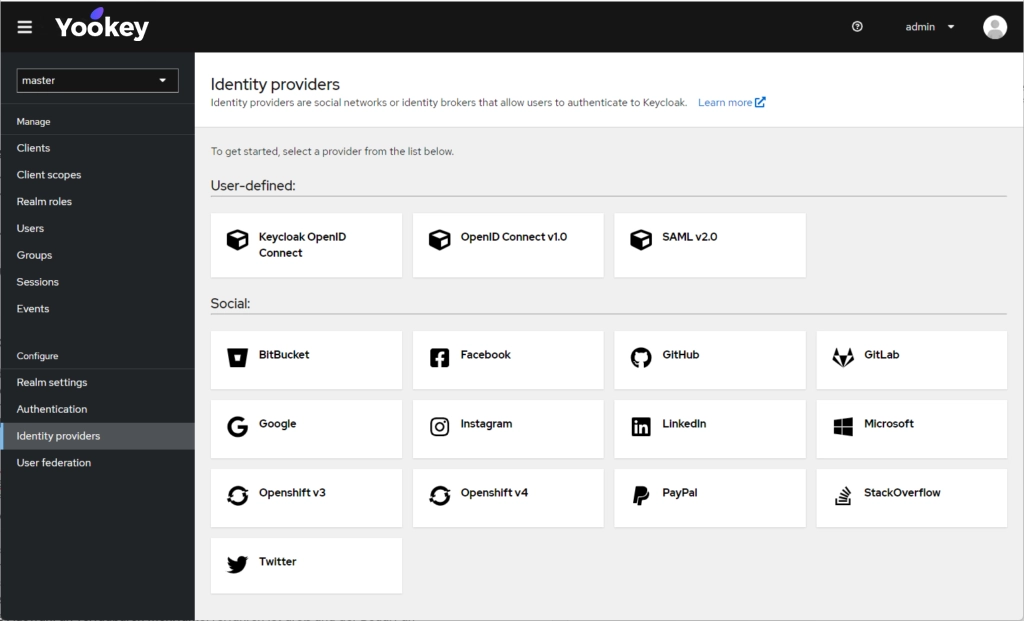
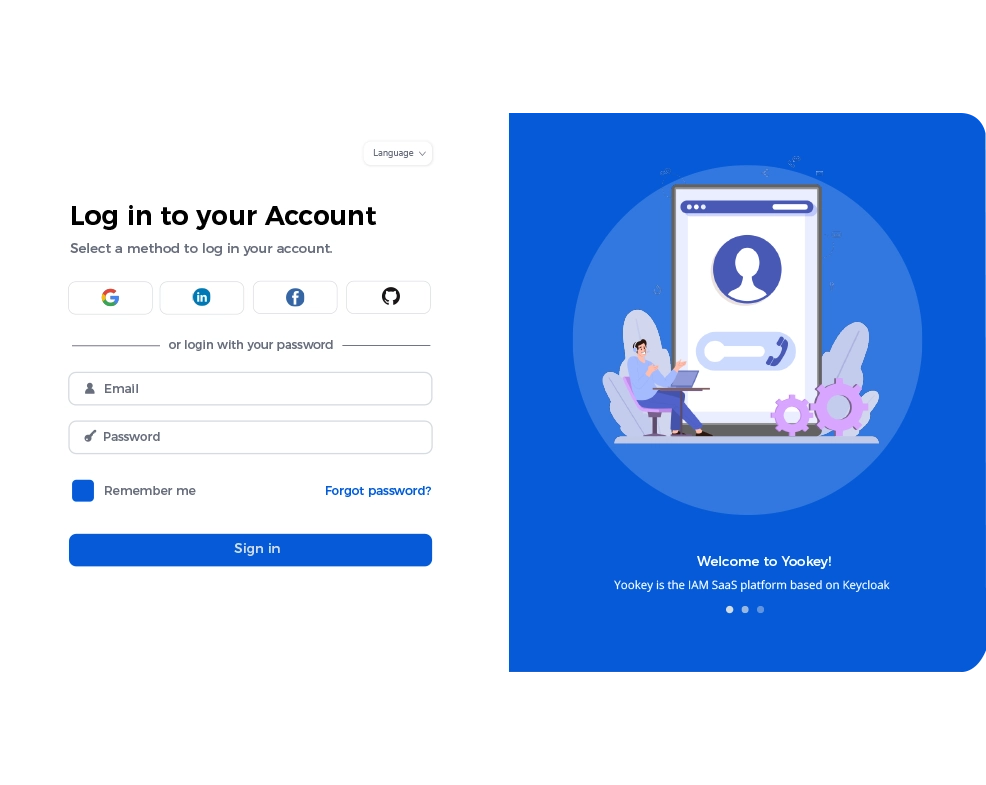
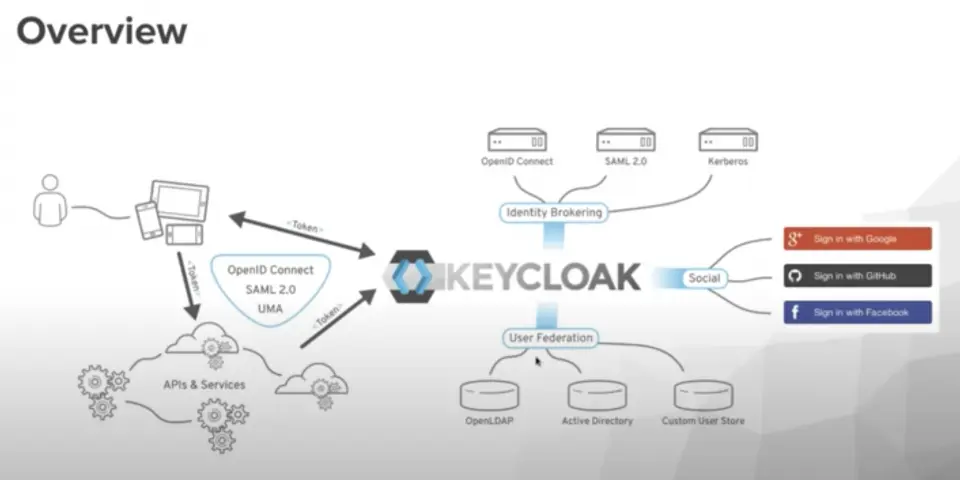
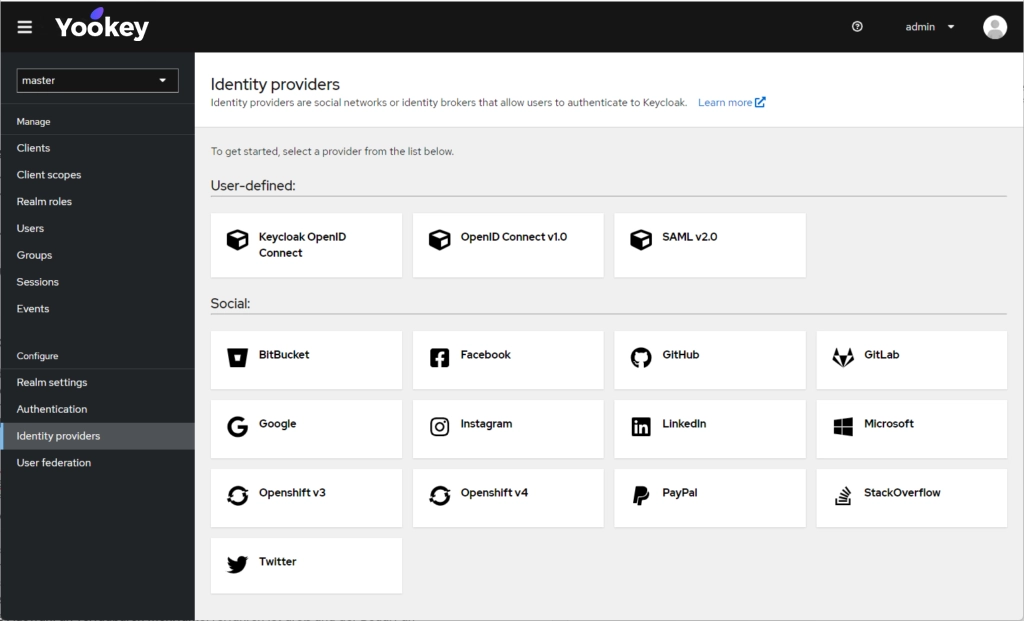
Yookey is a Keycloak-based SaaS (Software as a Service) solution. The platform centrally manages Single Sign-On (SSO), LDAP/Active Directory integration, and supports standard protocols such as SAML and OpenID Connect.
Regarding recovery and security tools, Yookey offers:
- Session Management: Allows administrators to directly manage user sessions, a crucial tool during incidents for revoking active access.
- Strong Authentication (MFA and Passkey): Supports advanced authentication and recovery methods, including SMS, email, physical tokens, authentication apps, and the latest Passkey technology. It also integrates specifically with SPID and CIE (via Yookey ID) to ensure verified user identity.
Parla direttamente con il nostro team per ulteriori informazioni.