Identity Governance vs IAM: differences and how they integrate in IT security
- What is Identity Governance (IGA)?
- What is Identity Management (IAM) and what it is used for
- How Access Governance works?
- Difference between Identity Governance and Identity Management
- Identity Governance and Identity Management: two complementary systems
- Yookey, the Identity & Access Management software

What is Identity Governance (IGA)
Identity Governance and Administration (IGA) is a cybersecurity discipline focused on control, compliance, and management of access rights of digital identities within corporate systems.
Its main objective is to ensure that every user has appropriate, traceable, and compliant access with security and privacy regulations. IGA in fact makes it possible to answer three fundamental questions: who can access, what they can access, and for how long.
In modern IT environments, often hybrid and complex, IGA is essential to:
- reduce the risks of unauthorized access
- prevent breaches related to compromised credentials
- keep permissions always aligned with company policies
What is Identity Management (IAM) and what it is used for
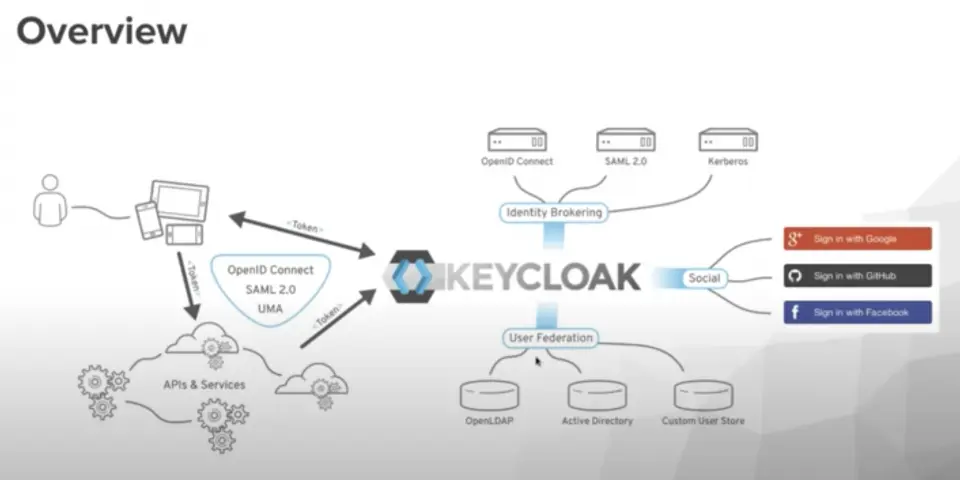
Identity Management (IAM) is a set of technologies, processes, and rules that allows the management of digital identities and control of access to corporate resources.
Its purpose is to ensure that only authorized users, devices, or applications can securely access systems, networks, and data, with permissions appropriate to their role.
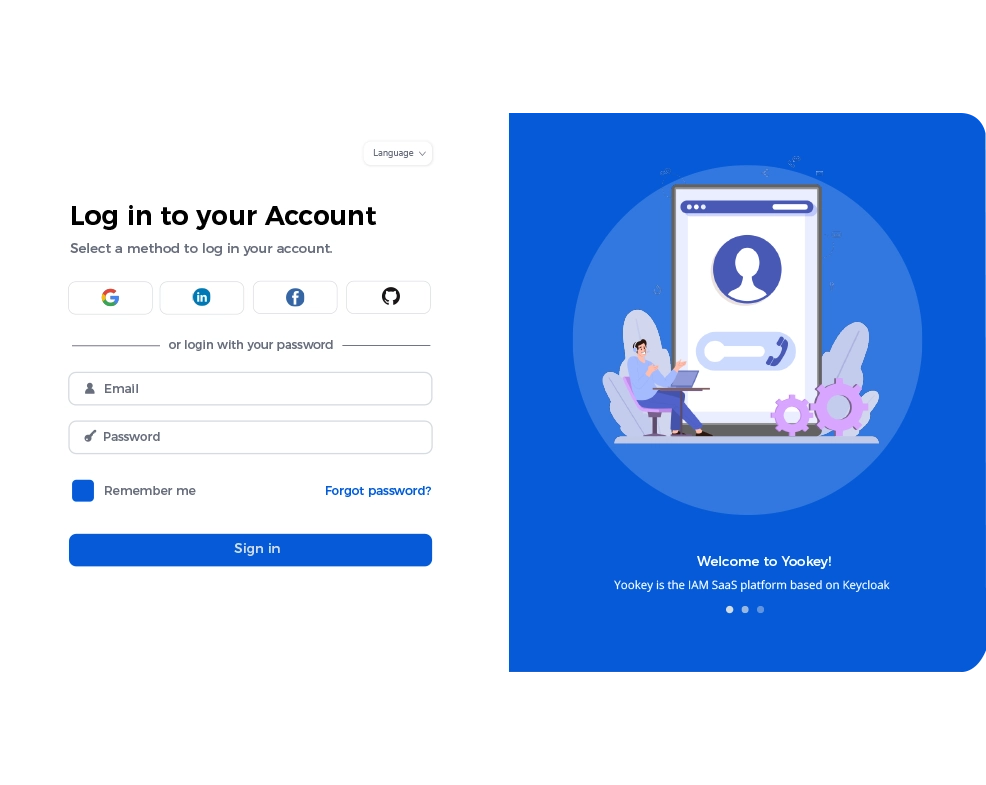
In addition to security, IAM also improves the user experience thanks to features such as Single Sign-On (SSO), which simplifies access to applications without compromising system protection.
Ready-Made Templates
Are you looking for an IAM system?Visit the Yookey website to discover the available solutions
How Access Governance works?
Access governance is a continuous control layer that ensures that the rights assigned to users always remain correct over time.
This process is based on several key mechanisms, including:
- RBAC (Role-Based Access Control): assigns permissions based on the business role
- SoD (Segregation of Duties): prevents conflicts of interest by separating critical tasks among multiple users
- Access reviews and periodic certifications: managers verify and confirm or revoke access
In addition, governance generates detailed audit trails that make it possible to demonstrate compliance with regulations and internal policies.
Difference between Identity Governance and Identity Management
The main difference between IAM and IGA concerns role and purpose.
- Identity Management (IAM) focuses on the operational management of access: authentication, account management, and technical control of authorizations.
- Identity Governance (IGA), on the other hand, deals with the supervision and control level, verifying that access is appropriate, justified, and compliant with company rules.
In summary:
- IAM answers: how a user accesses and what they can do
- IGA answers: whether that access is correct, necessary, and compliant
Identity Governance and Identity Management: two complementary systems
IAM and IGA are not in competition, but two complementary components of a single identity security strategy.
For example, when an employee changes role:
- IAM operationally manages the modification of access (assignment and revocation of permissions)
- IGA verifies that these changes are consistent with company policies and ensures traceability for audits
Together, these two systems combine operational efficiency (IAM) with control and compliance (IGA).
What is the difference between authentication, authorization, and governance
These three concepts represent different levels of access management:
- Authentication
It is the process that verifies the user’s identity through credentials such as passwords or multi-factor authentication. - Authorization
It occurs after authentication and determines which resources a user can use and with which permissions. - Governance
It is the strategic control level: it defines access policies, monitors compliance, analyzes risks, and periodically verifies that assigned permissions are still appropriate.
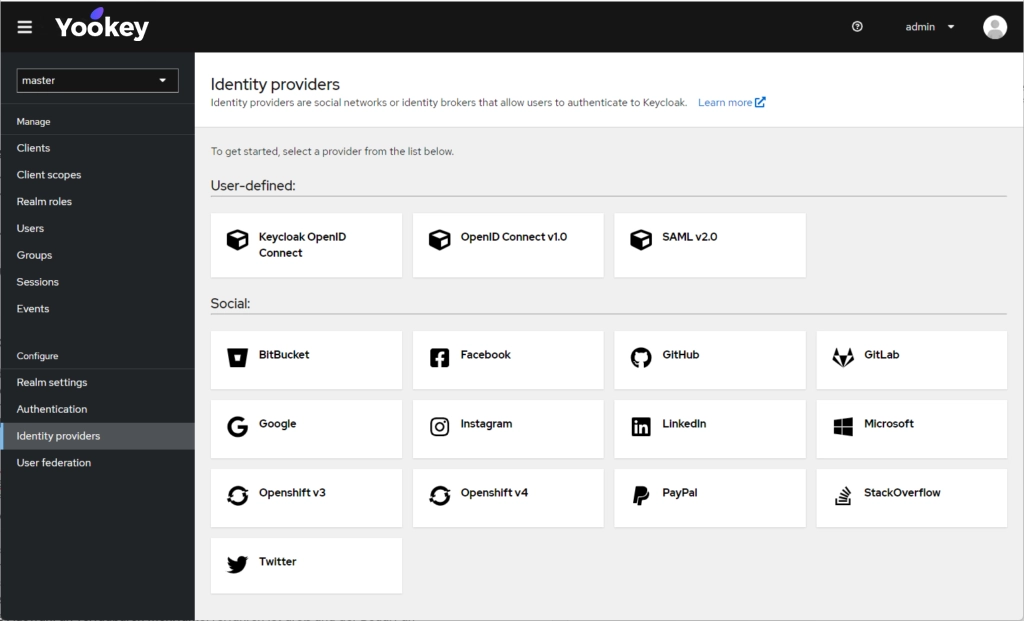
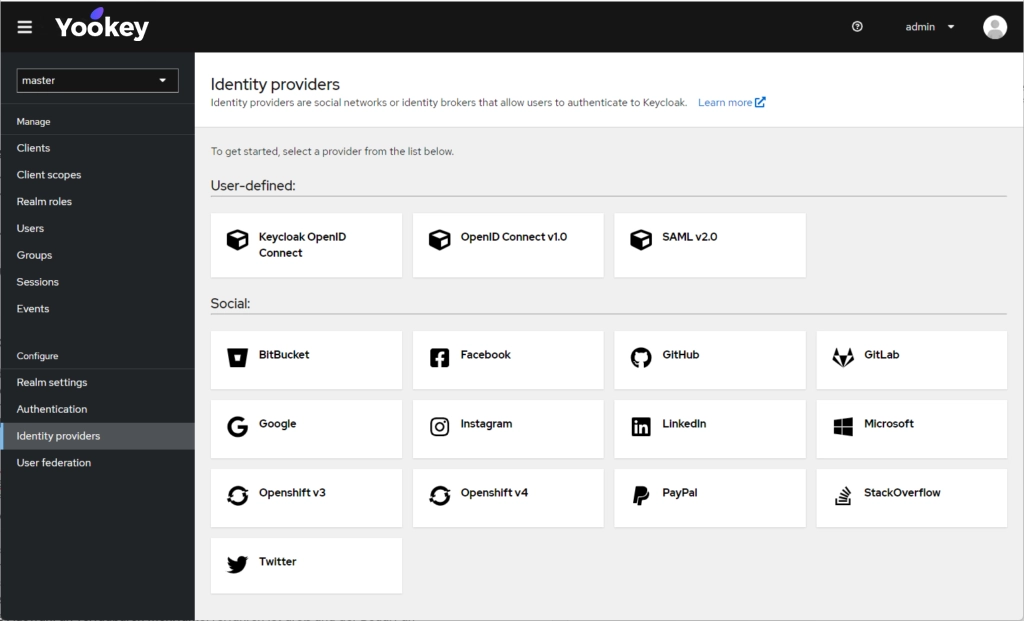
Yookey, the Identity & Access Management software
Yookey is an Identity and Access Management (IAM) system based on processes and technologies that securely manage digital identities and access to resources and services.
Yookey ensures secure and efficient onboarding and offboarding processes, thanks to integration with Single Sign-On (SSO) and automation of access management.
During onboarding, users are automatically assigned the correct permissions based on their role, with the addition of multi-factor authentication (MFA) to ensure a high level of security.
At the end of the employment relationship, offboarding is managed in a centralized way: all access is revoked from all connected applications, eliminating the risk of orphan accounts or residual privileges.
The entire lifecycle is fully tracked and documented, ensuring compliance with regulations such as NIS2 and ISO 27001.
Speak directly with our team for further information.